Secure browsing and real-time protection for all Android and iOS devices
Simply block unwanted apps
Theft protection makes sure that your company data is safe

What Is Mobile Device Management?
Mobile Device Management (MDM) gives you control of the company's mobile device landscape. With our MDM solution, you centrally manage the security of your iOS and Android mobile devices in accordance with current data protection guidelines. Thanks to cloud connectivity, the devices always receive the latest protection updates, even outside the company network.
Are you using Enterprise Mobility Management (EMM)? Our MDM is compatible with it - for even easier installation and management.
Included in G DATA Endpoint Security at no extra charge.
How Mobile Device Management makes your work easier
- Mobile devices in view
- Add devices easily
- Roll out settings centrally
- Set profiles
- Clear recommendations for action
- Theft protection
- Block unwanted apps
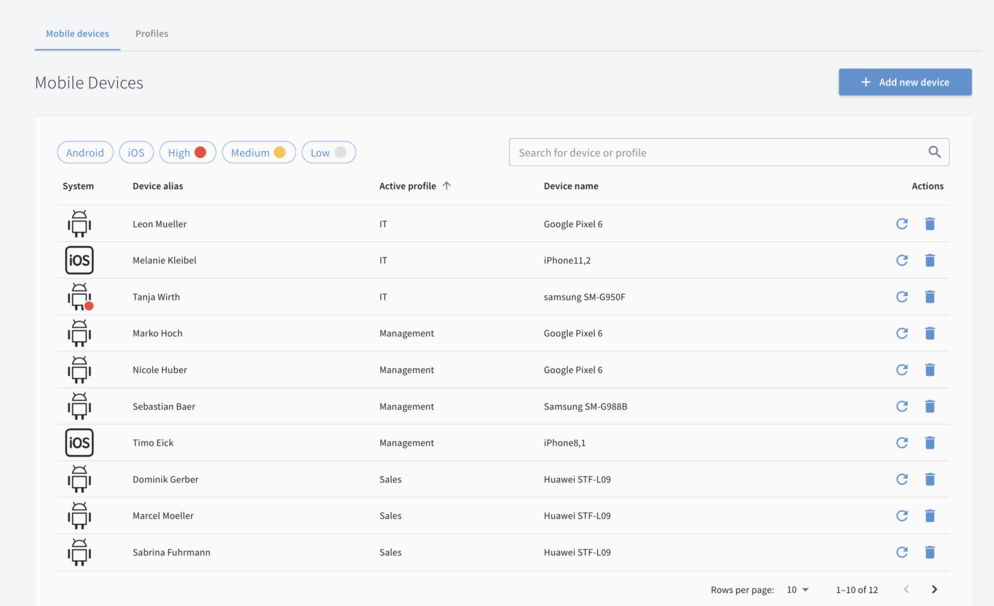
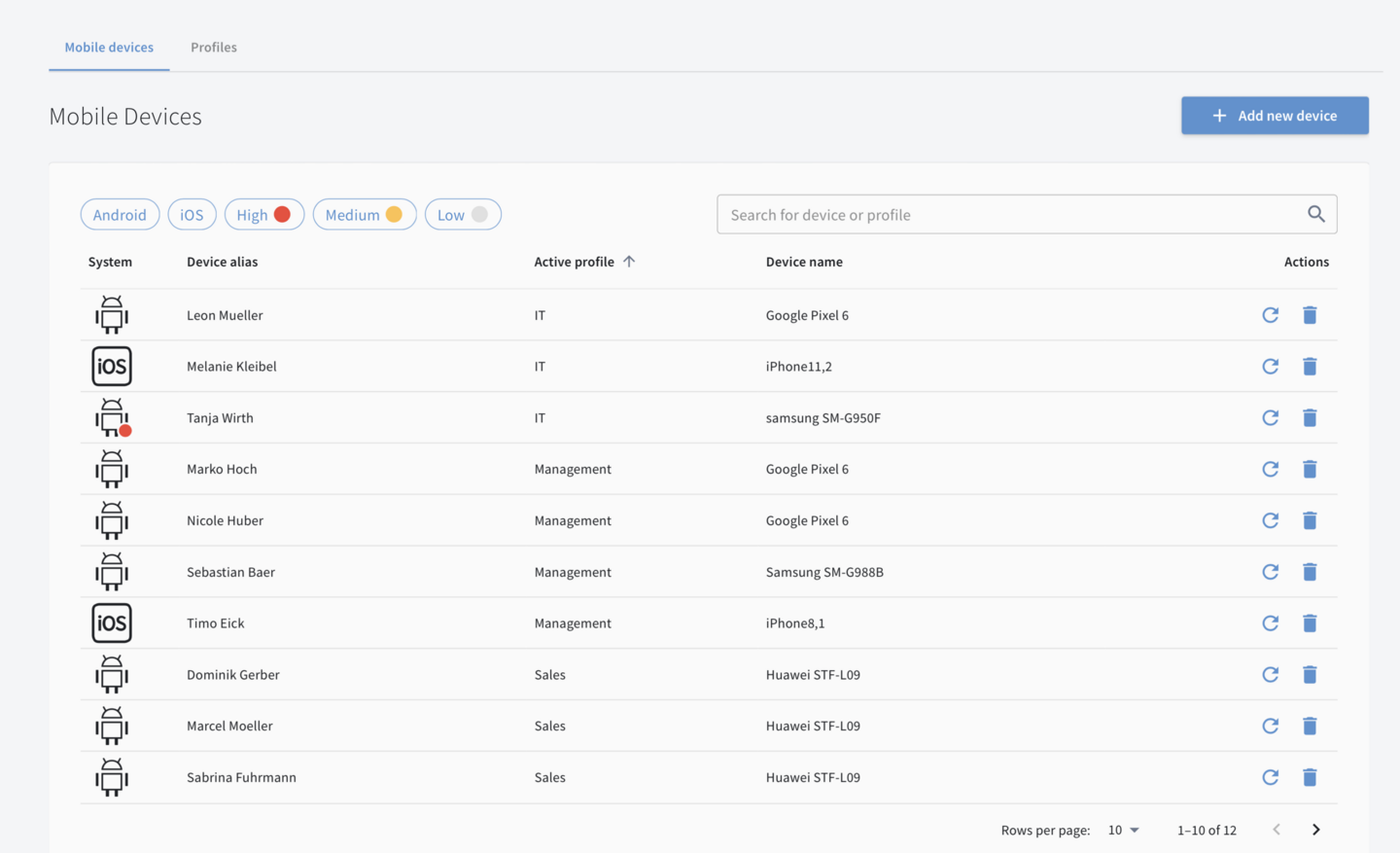
Mobile devices in view
Keep an eye on the security of your mobile devices in the central dashboard.
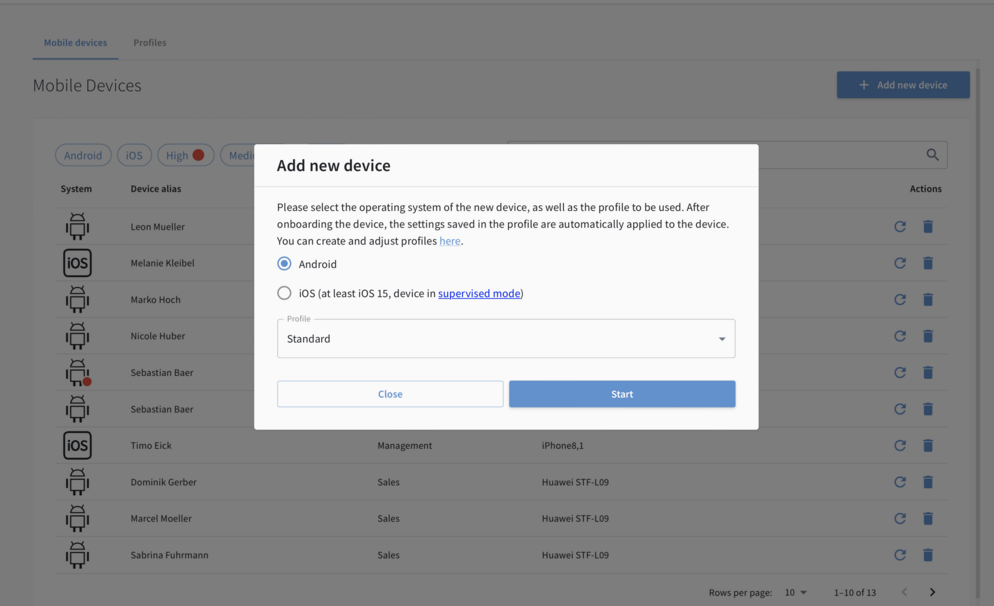
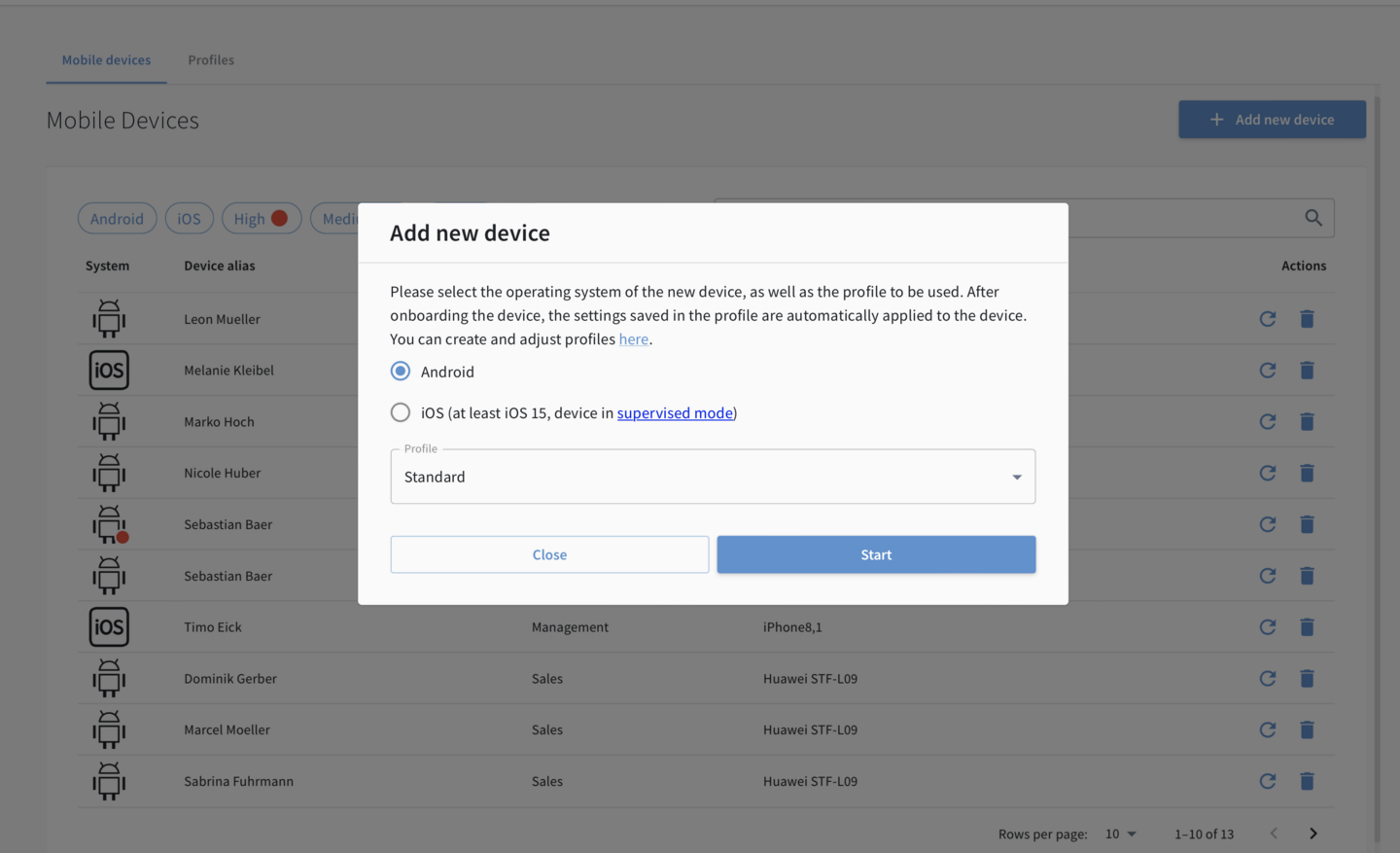
Add devices easily
Save time by conveniently adding new devices from the dashboard.
Roll out settings centrally
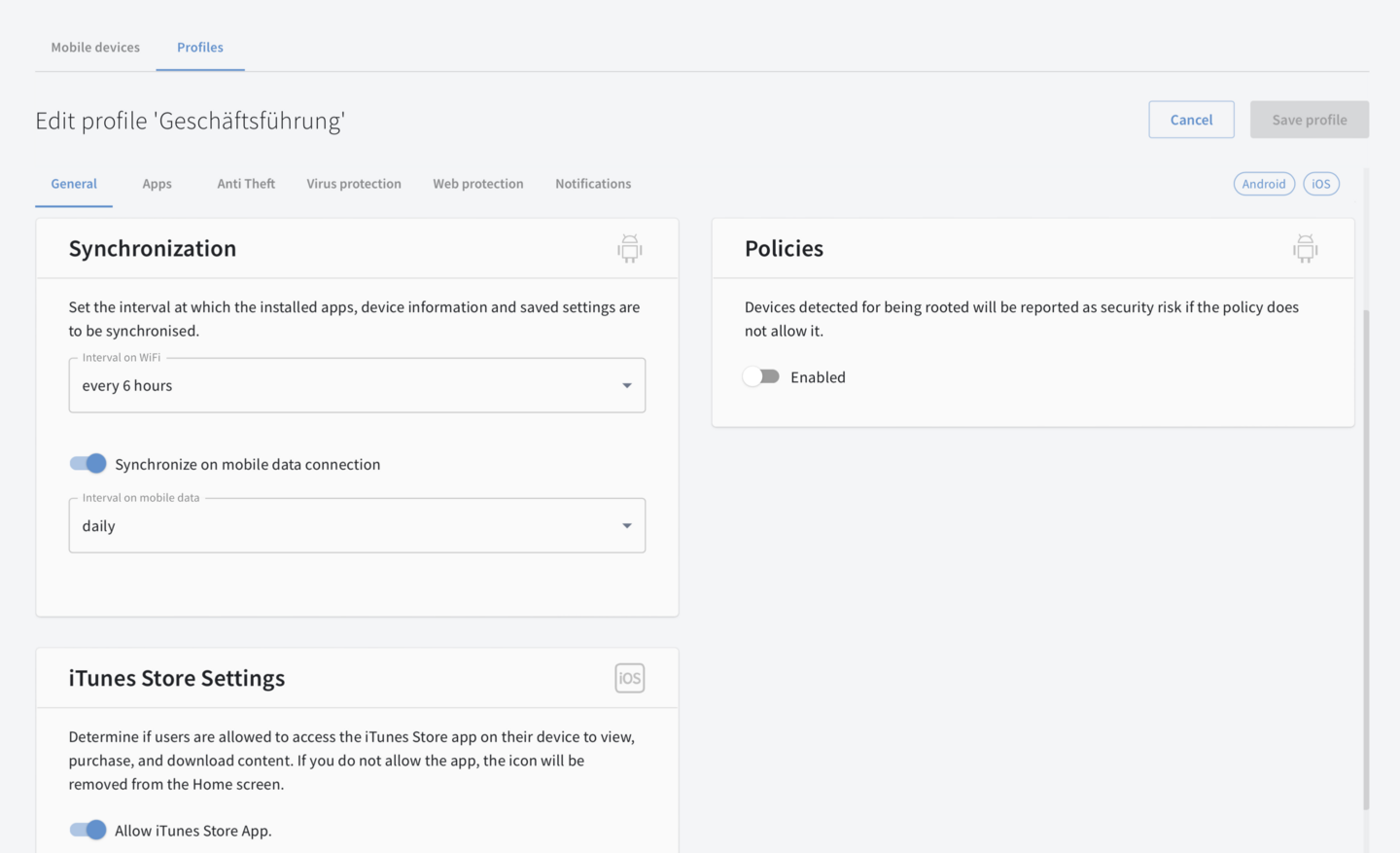
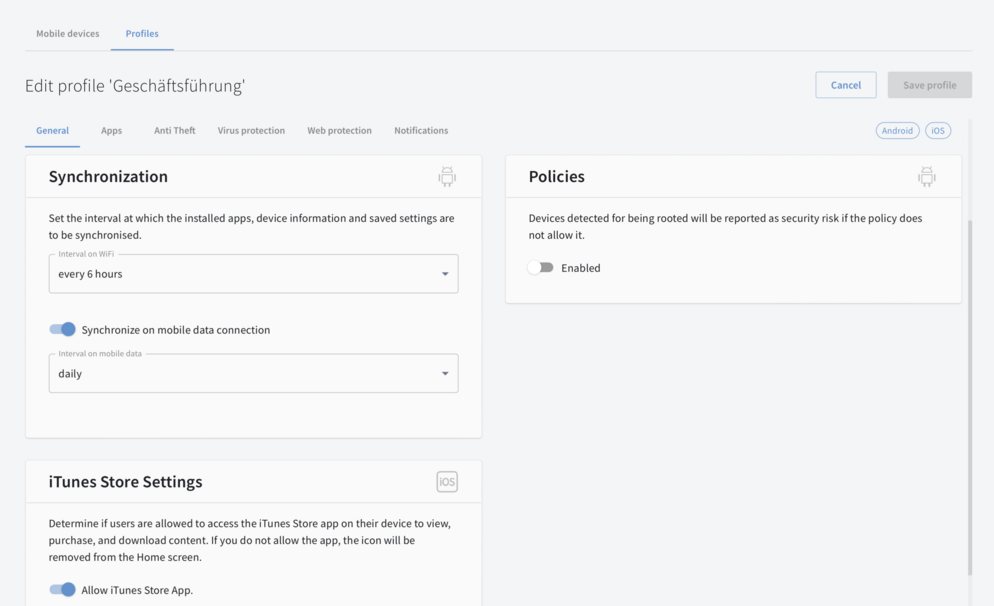
Easily roll out new security settings and policies centrally to all devices.
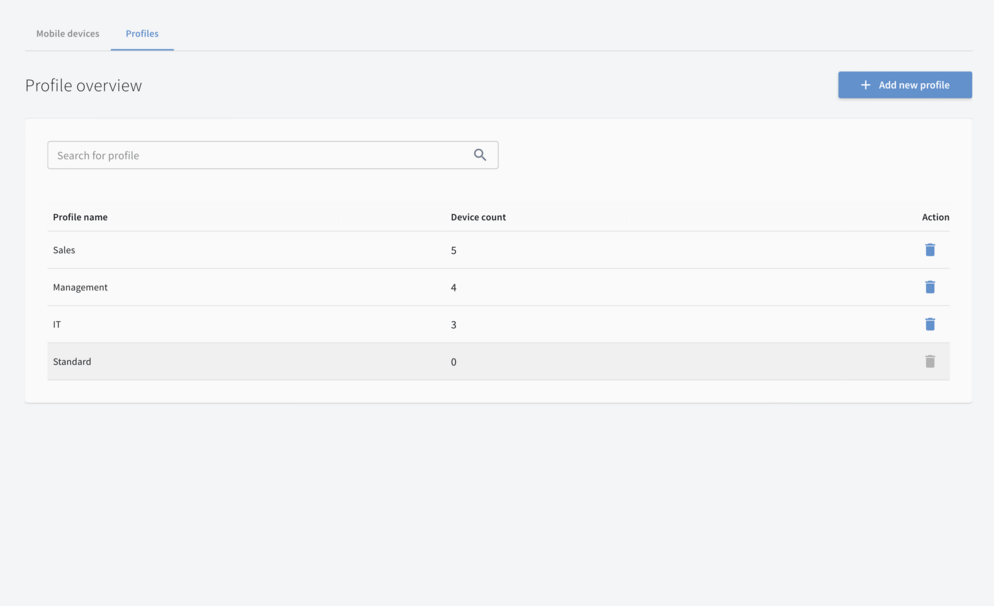
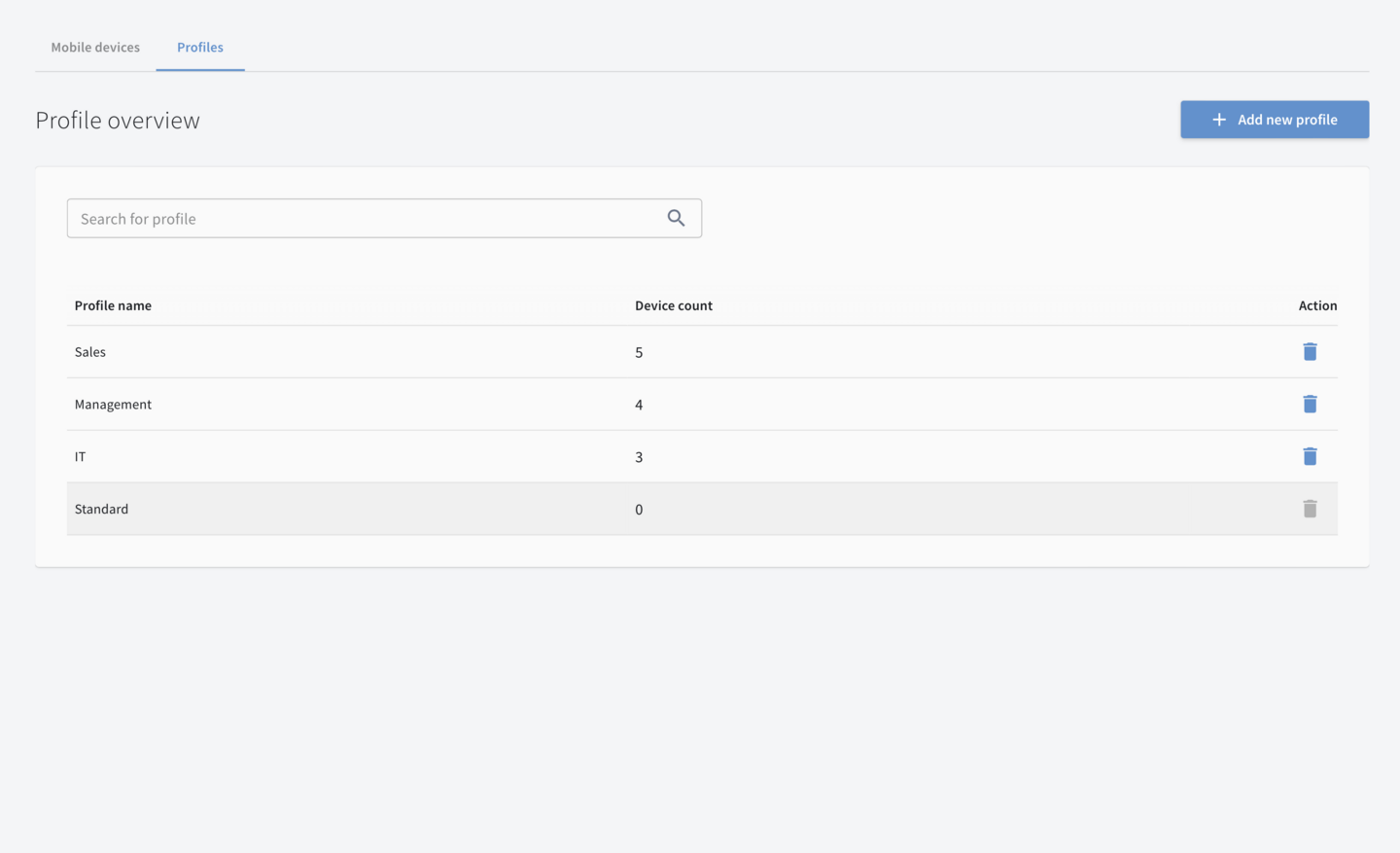
Set profiles
Assign mobile devices from different departments or sites to individual profiles, based on security level.
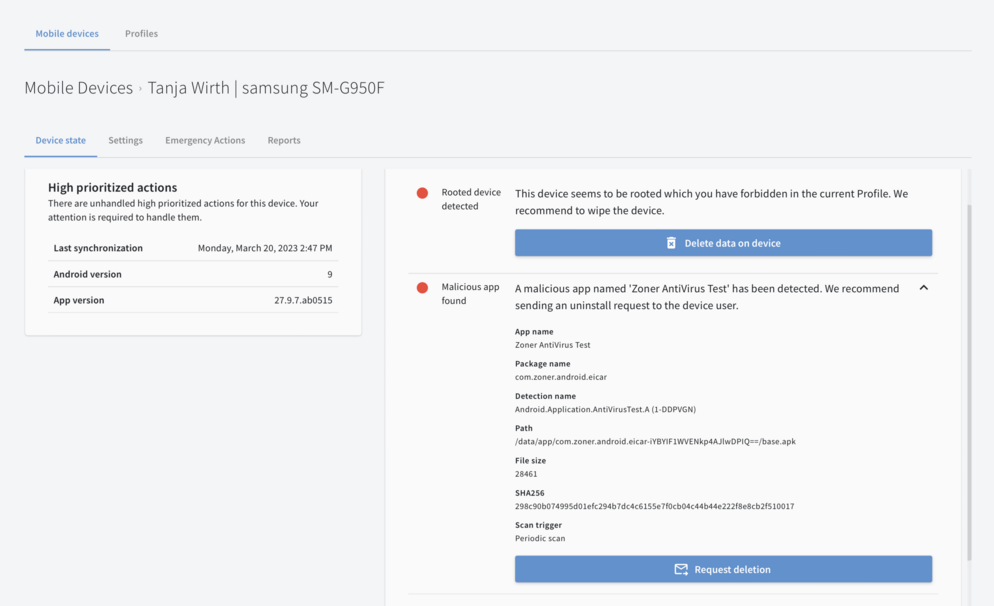
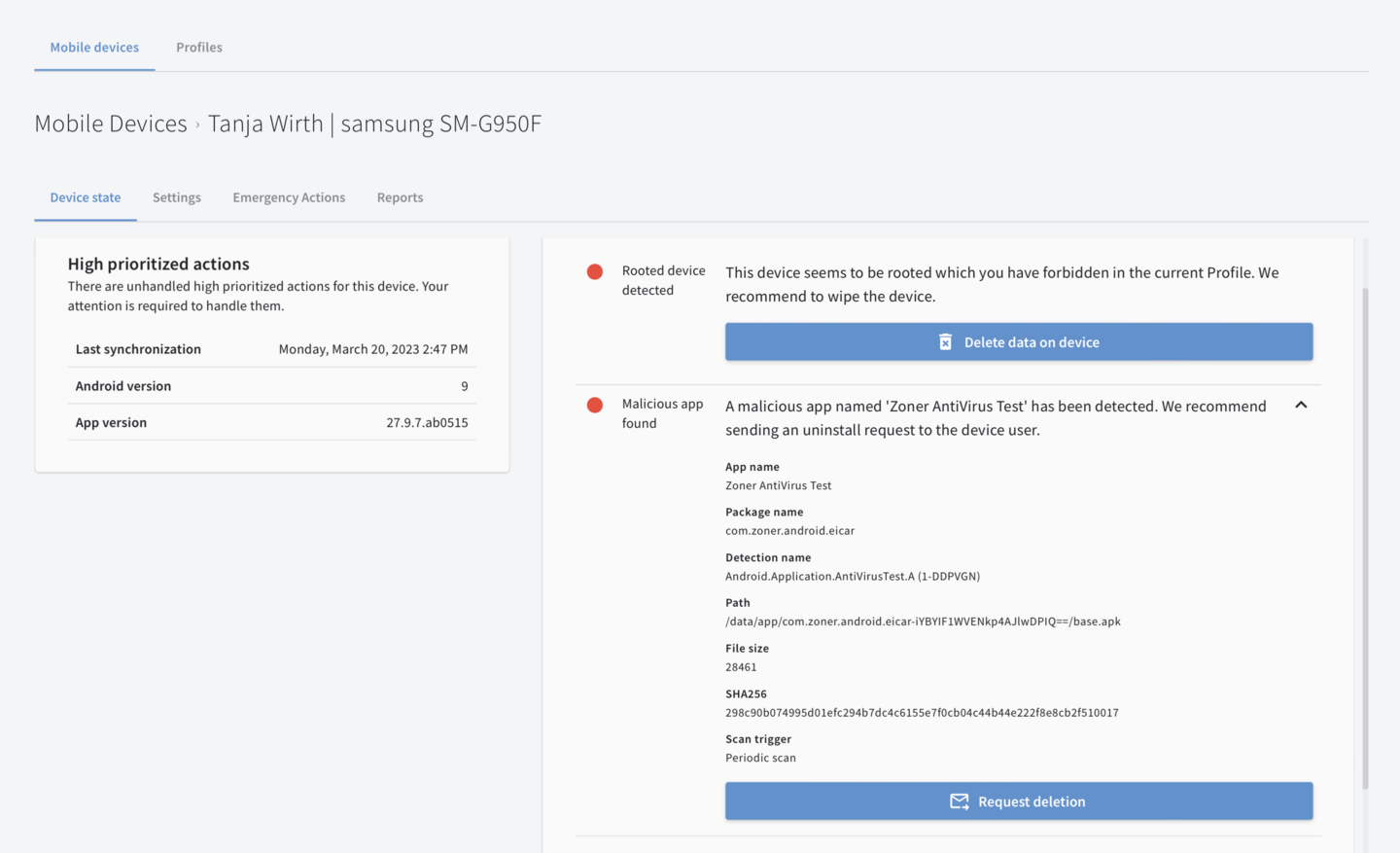
Clear recommendations for action
Identify and remediate security issues as they arise.
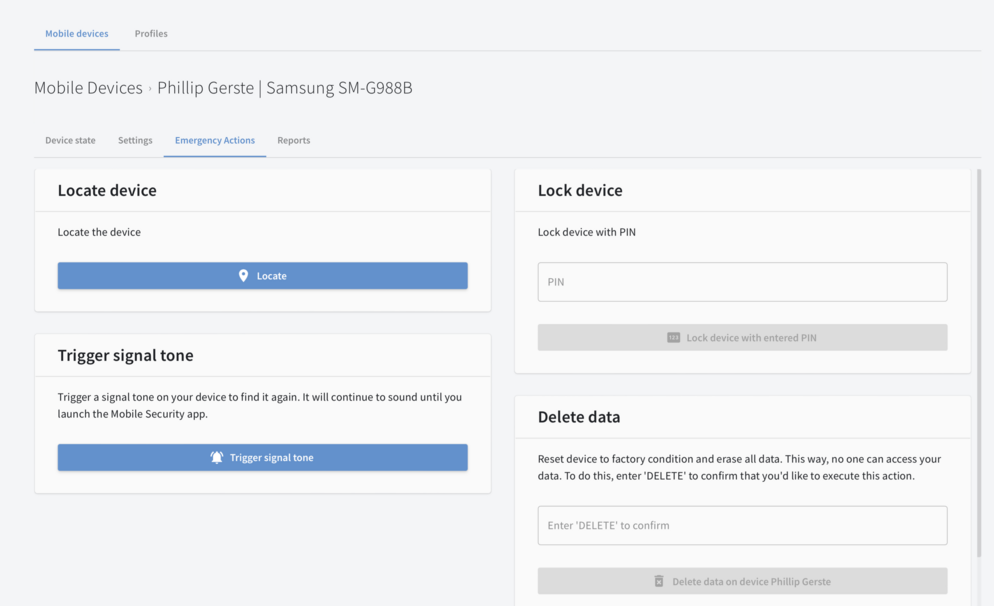
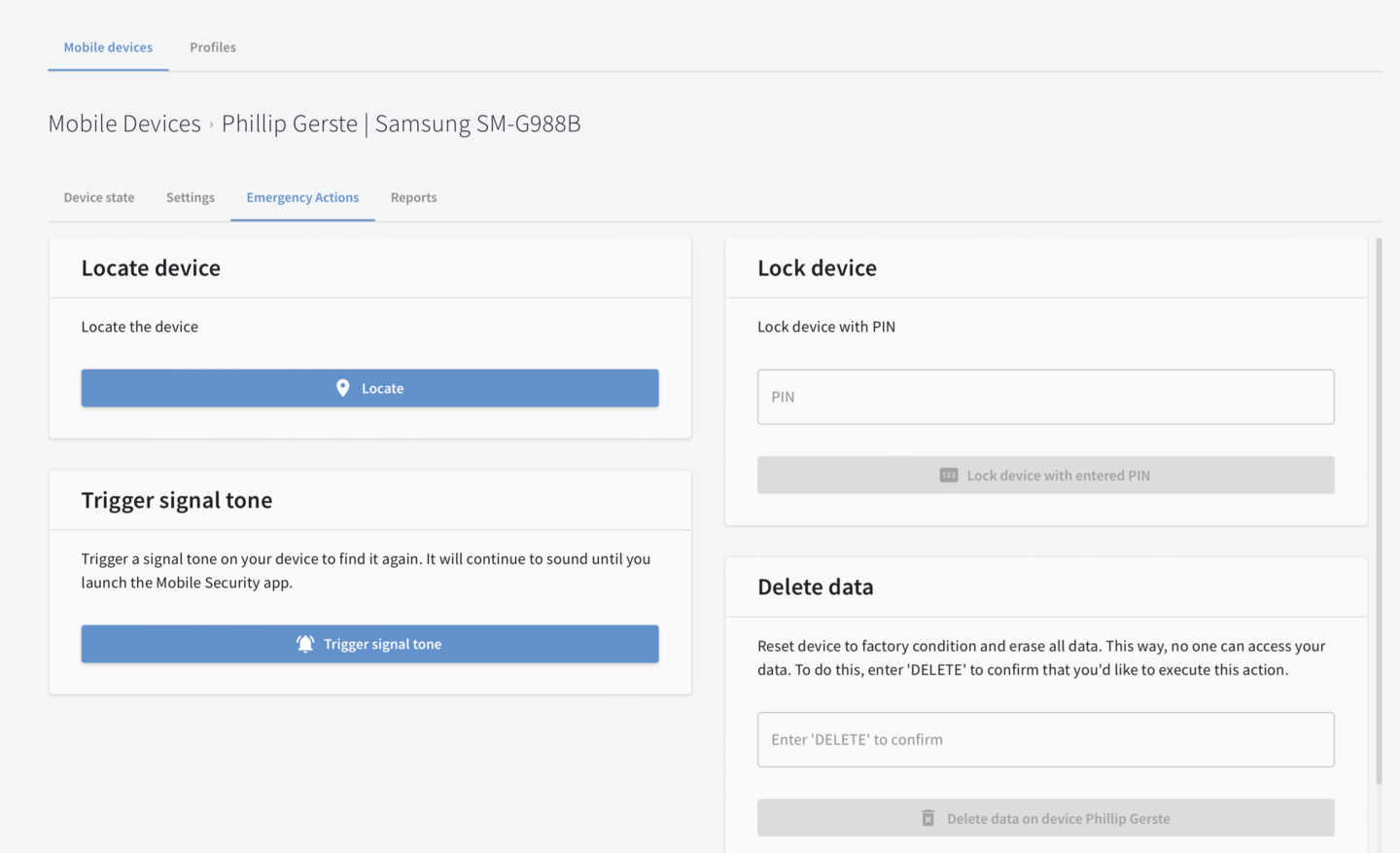
Theft protection
Protect sensitive files from unauthorized access: Remotely locate, lock or wipe devices.
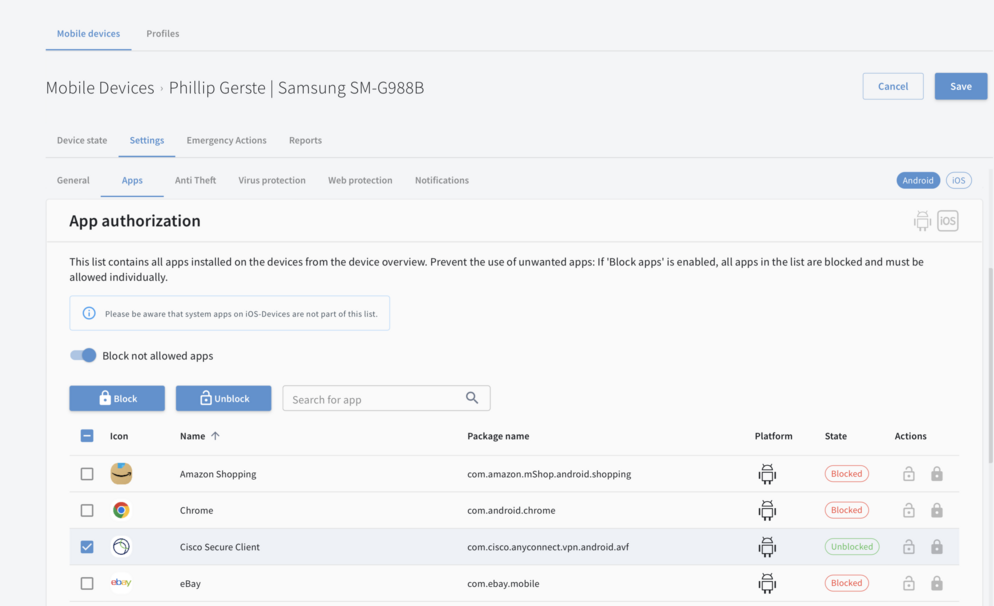
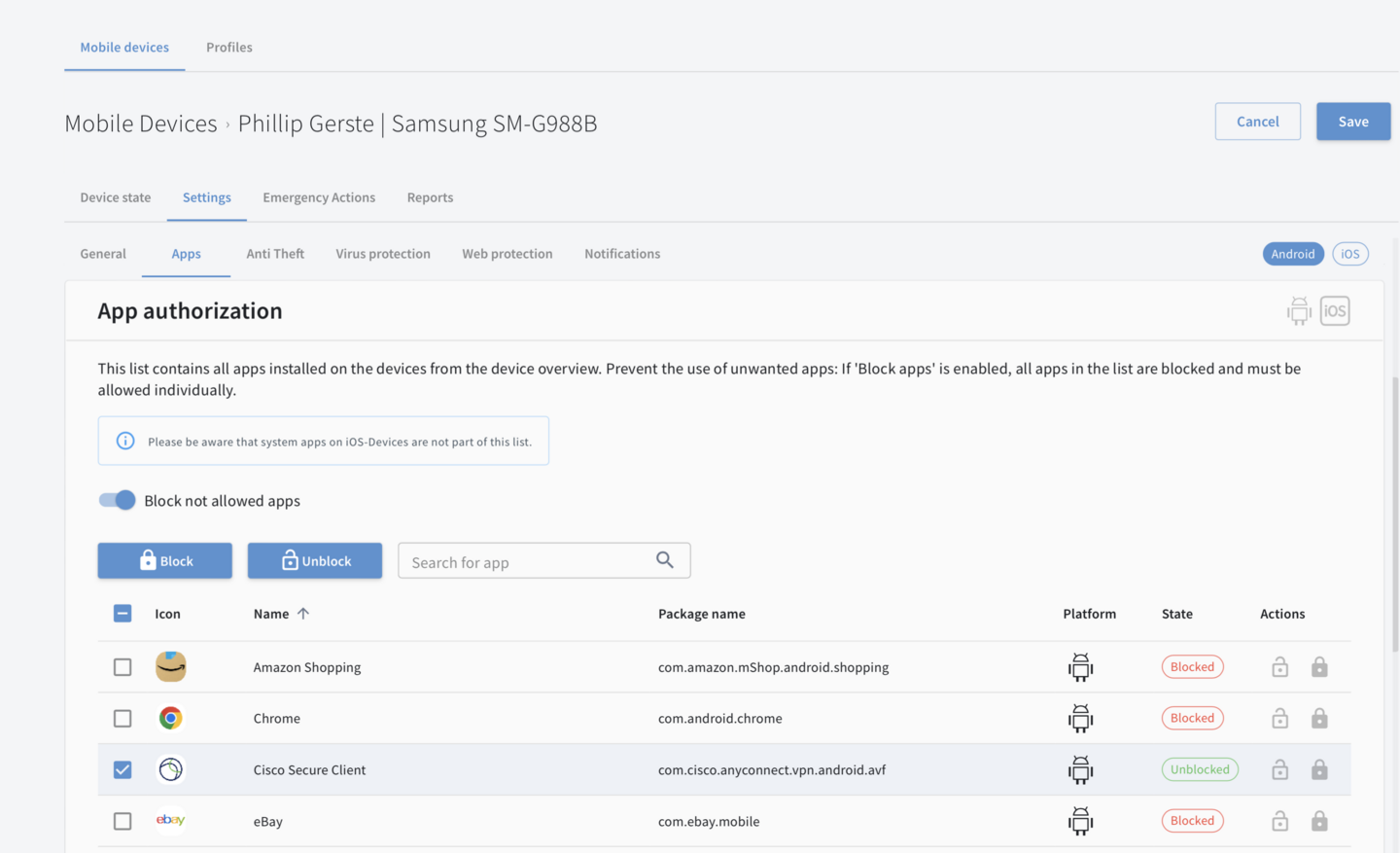
Block unwanted apps
Prevent the use of unwanted apps by blacklisting and whitelisting.
Tested. Proven. Excellent.


24/7 Support
Our experts are always there for you by phone or email, 24 hours a day, 365 days a year. Completely free of charge.
Complete Protection for Companies
Mobile Device Management Is Part of Every G DATA Endpoint Security Business Solution
No matter which G DATA Endpoint Security business solution you choose, our comprehensive Mobile Device Management (MDM) software is included at no extra charge. Protect your company data from unauthorized access from external sources.
Try it now free of charge More information on G DATA Endpoint Security

Why an MDM Solution is important
Smartphones and tablets are being used to complete security-critical tasks with ever-greater frequency – both at home and in the office. Devices that lack adequate protection are therefore a high risk for your company’s IT security. In 2021, G DATA experts counted almost 2,5 million new Android malwares – and that number is rising. Our MDM solution protects your company against this danger and offers additional features that make it easier for you to manage all the mobile devices in your business. G DATA’s Mobile Device Management software increases security in your company and also complies with data protection provisions set out in the European General Data Protection Regulation (GDPR).