Anyone who believes that the risk of a cyber attack has decreased in view of the falling numbers is deceiving themselves. Currently, attackers are increasingly gaining access to companies via unsecured remote access or vulnerabilities in publicly available services, as the attack by the Hafnium group via a vulnerability in Exchange servers has shown. Trained staff, along with established processes, are needed to improve IT security in companies. In this regard, those in charge need to act quickly. Otherwise, it is only a matter of time before they fall victim to an attack.
G DATA threat report: Attackers exploit vulnerabilities in publicly available services
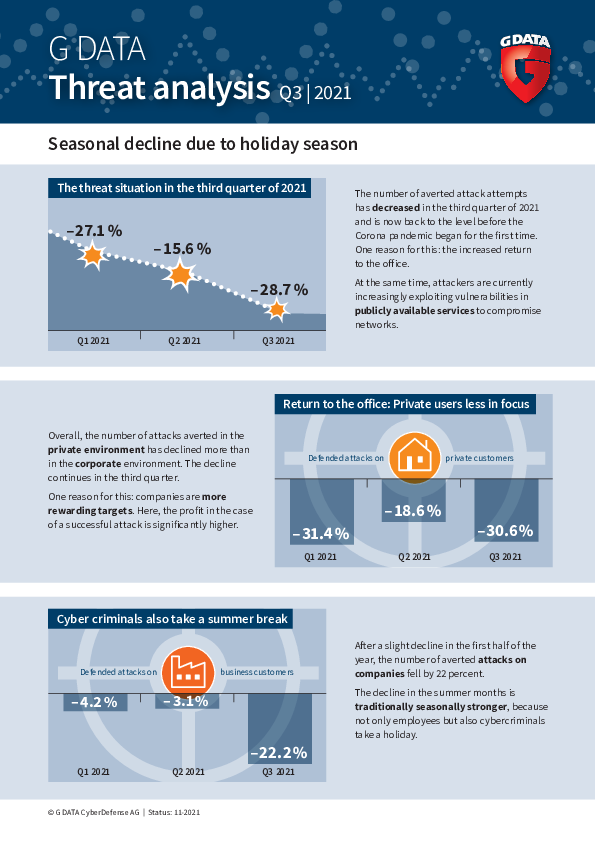
Seasonal decline due to holiday period
The number of averted attack attempts continued to fall in the third quarter of 2021. This is reflected in the current threat report from G DATA CyberDefense. One reason for this is that more employees are returning to the office. At the same time, attackers are increasingly exploiting vulnerabilities in publicly available services currently with the aim of compromising networks.
The number of averted cyber attacks in the third quarter of 2021 is back where it was before the start of the coronavirus pandemic. The number fell by 28.7 percent compared to the second quarter. The reasons for the decline are that, traditionally, the number of attack attempts is seasonally lower in the summer months than at other times. In addition, employees returning to the office after working from home are also contributing to normality and leading to falling numbers. At the beginning of the pandemic especially, the numerous poorly secured computers in the private environment were easy prey for cyber criminals. Overall, numbers in the private environment have declined more than in companies. Within three months, the number of averted attack attempts on consumers fell by more than 30 percent. In the business environment, the number fell by 22 percent.

Coinminers are here to stay
The latest analyses show high coinminer activity for the third quarter of 2021. In this case, cyber criminals use the computing power of other people's computers to generate Monero or other cryptocurrencies. While criminal intruders make money from this, users must pay for increased electricity costs and use a computer with limited performance. When criminals exploit the computing capacities of companies by compromising server farmers or cloud instances, the financial damage is great.
Malware: old acquaintances rather than new dangers
The current threat report shows that attackers are continuing to rely on established malware. Between June and August 2021, they were particularly active with malware - Glupteba, Agent Tesla and STOPRansomware - that has already been active for several years. Cyber criminals are developing these further and are also working on hiding the malicious code from security solutions. To do this, they usually use so-called packers, which make the malicious core unrecognisable. Using automated tools, they can send new waves of attacks through the network almost every second.
Rootkits: there's life in the old dog yet
During the year, cyber criminals have again been making increasing use of rootkits. These are experiencing a renaissance after several years. Rootkits are used alongside malware such as ransomware or droppers and ensure that malware or spyware remains undetected on the system for as long as possible, or that criminal groups can manipulate the computer remotely. In doing so, they have far-reaching rights at the administrator level, so that they can access every function of the operating system. On top of that, rootkits can hide most traces of their existence very well.

In view of the current threat situation, companies need up-to-date protection technologies to ward off any devious attack attempts. At G DATA, we use technologies such as machine learning to ensure effective proactive protection.
Media:
Files:
- G_DATA_Bedrohungsreport_A4_Q3_2021-EN.pdf (652,74 KB)
- G_DATA_Tim_Berghoff_MG_0227_300dpi.jpg (6,76 MB)